iptables contains 5 tables by default. Tables contain chains (rulesets) and rules.
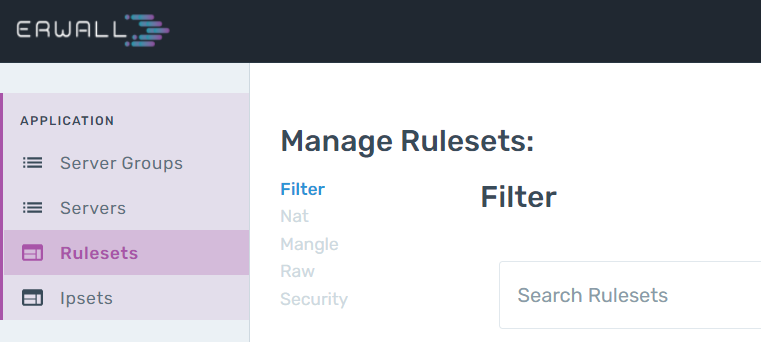
A ruleset can be defined as rules that come together in an ordered group format. It is the equivalent of the chain structure in IPTables in the ERWALL interface. Rulesets can be used in the JUMP part of other rules. The chain structure of IPTables consists of rulesets that are run sequentially according to the conditions. The ruleset in the JUMP part of a rule that is operated and whose condition is met will be switched to and the rules in that ruleset will continue to be operated sequentially.
An iptables rule checks the validity of an IP package based on specified condition and performs an action according to that validation. The columns listed in the rule table are fields of an IP packet. Rules entered into a ruleset are executed sequentially. If the condition specified in the rule matches the package, the action in the JUMP section is performed. These actions are:
If a packet does not match any rule, then the policy of the built-in chain is operated. It can be either ACCEPT or REJECT. By jumping between chains and trying the rules, requests get accepted or rejected eventually and related actions are taken for the packet.
IPSet is the structure that can be used to group IP addresses with similar attributes. IP Addresses may differ in terms of source company, whitelist, ISP. IPSets can be used when defining rules. For example, when you want to block the IPs in your blacklist, instead of entering these IPs one by one, you can create an IPSet and define your rule over it. Likewise, a user who wants to block all IPs belonging to Amazon can define rules by adding these IPs to an IPSet. Since the IPSet structure performs a search over a hashmap, it provides benefits in terms of both computational complexity and ease of use.